Table of contents
Data recovery isn’t just helpful for IT companies and private users; law enforcement officials have consistently sought data recovery services for the purposes of gathering evidence and convicting criminals. The cases tend to involve various kinds of white-collar crime like embezzlement and bankruptcy fraud, but even murder convictions have been made possible by evidence gathered through the recovery of “lost” or deleted data. This process is part of a larger criminal investigation tool called computer forensics. Computer forensics provides the legal system with a way to identify, extract, document, preserve, and interpret computer data for the purpose of bringing a criminal to justice. Although the list goes on and on, here are five interesting instances in which data recovery solved the case.
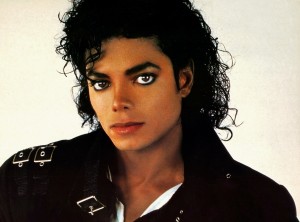
The death of the king of pop
When Michael Jackson died of a massive overdose of the anesthetic propofol in June of 2009, authorities were alarmed to find that he had been prescribed the dosage by his physician, Dr. Conrad Robert Murray. Murray wasn’t convicted of involuntary manslaughter through computer forensics alone, but some of the most damning evidence brought against him was collected from his computer’s hard drive; the prosecutors presented the computer’s medical documentation of the doctor’s prescription of lethal amounts of propofol, and the jury took only eight hours to convict him.
Finding the strangler
Also known as the BTK (Bind, Torture, Kill) Strangler, Dennis Rader murdered a number of women and evaded police identification for over 16 years. He even taunted the police who sought him and was known for sending letters and poems to the department, supposedly for his own entertainment. It looked as if the BTK Strangler case would never be solved until Rader broke almost a decade of silence and sent authorities a floppy disk containing a Word document in 2004. It only took a few hours for computer forensics experts to discover metadata on the disk that connected it to a “Dennis” at Christ Lutheran Church. Rader eventually admitted to his crimes.
Stopping a terrorist
When UK computer experts searched a computer owned by Krenar Lusha, they discovered a number of downloaded instructions for committing major crimes; among them were directions for how to make suicide belts and other explosives. The experts were also able to look through his history of live chats, finding his discussions of being a terrorist and hoping to witness the death of Americans and Jews. Fortunately, Lusha was taken into custody before his aspirations could be made a reality.
Discovering a murder
Extensive research executed on the computer of Matt Baker led authorities to believe that his wife’s suicide was actually a murder. She had overdosed on sleeping pills and left a suicide note, circumstances which led most to believe there was nothing sinister behind the tragic turn of events. However, four years of in-depth investigation of Baker’s computer turned up the research he had conducted on a variety of pharmaceutical websites, specifically regarding sleeping pill overdoses. That research as well as other damaging evidence led to Baker’s sentence to 65 years in prison.
Email as evidence
Evidence for murder isn’t always found on the perpetrator’s device; in the case of the murder of Sharon Lopatka, authorities were unable to find any clues until they turned to the victim’s computer. Lopatka had sent hundreds of emails out to friends, family, and her eventual murderer. Only through analyzing the clues present in the emails saved to her hard drive did authorities trace the murder back to the assailant, Robert Glass.
In our digital era, computer forensics will only become more important when it comes to solving crimes. It just goes to show that data recovery isn’t only a convenient service; it’s playing an active role in the effectiveness of our justice system, and thus the safety of our society.